Flock Safety Cybersecurity: How We Protect Customer & Community Data
Flock CISO Chris Castaldo explains how layered defenses, specialized teams, and third-party partnerships protect customer data, while addressing recent misleading claims and offering a transparent look at how vulnerabilities are managed in the real world.
Flock Safety Cybersecurity: How We Protect Customer & Community Data
It has been three months since I joined Flock, and I am just as excited about the work we are doing today as I was on day one. The nonstop success stories from our customers fuel me every day to do the work required and expected of us in cybersecurity.
To recap, when I joined at the end of last year, I posted a blog on my why. Everyone has different things that drive them, and I wanted to share why Flock and why now. You can read that here, Why I Joined Flock: A Mission You Can Feel.
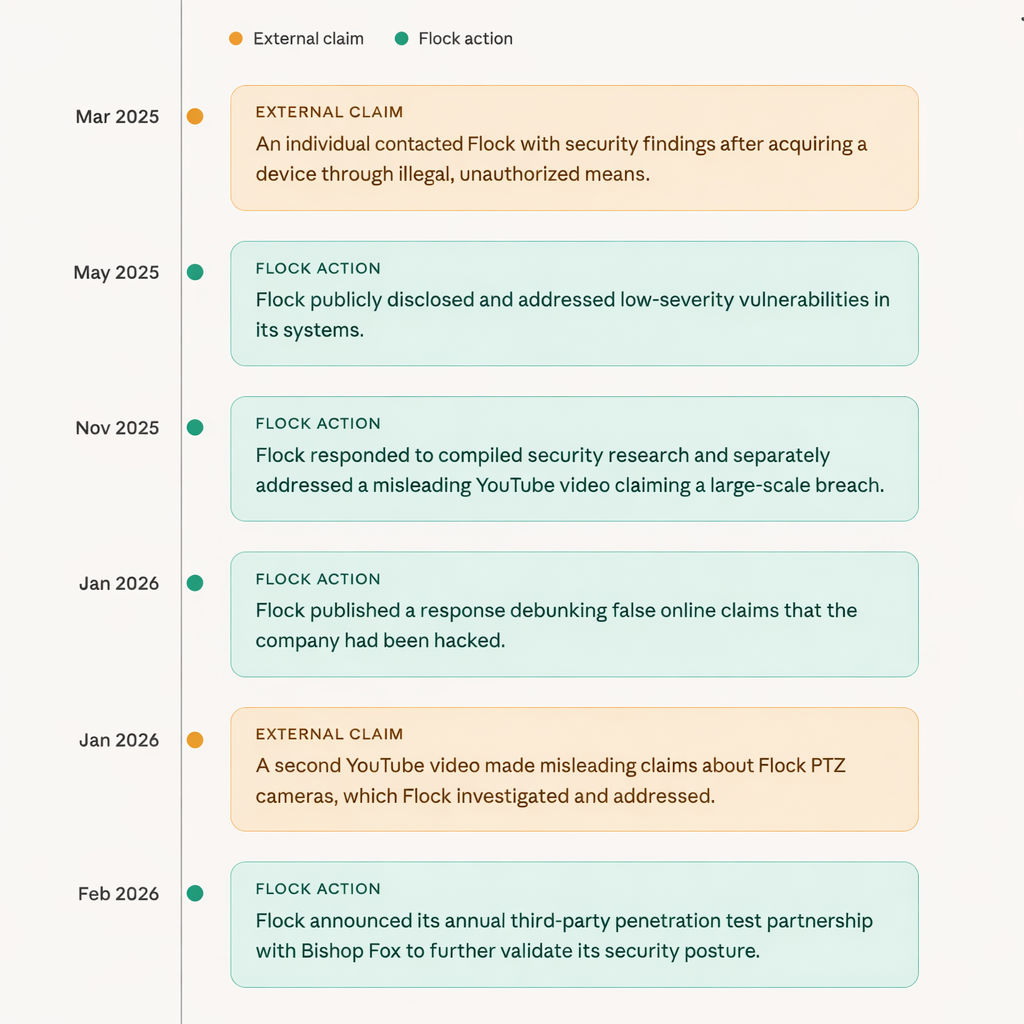
In January 2026, we responded to online claims that Flock had been hacked: “Has Flock Been Hacked?” As detailed in these blogs, these claims were false and/or misleading.
In February 2026, Flock announced that we had partnered with Bishop Fox to conduct our regular annual penetration test. I also shared more granular details about the engagement in a blog post, Holding Ourselves to the Highest Standard to Protect Community Data.
Prior to me joining the team, Flock also posted a response in November 2025 to publicly disclosed research, Response to Compiled Security Research on Flock Safety Devices.
In May 2025, Flock responded to publicly disclosed low-severity vulnerabilities: Gunshot Detection and License Plate Reader Security Alert.
Readdressing Misleading Claims About Cybersecurity at Flock
I want to be crystal clear: vulnerabilities are a part of the development process of hardware and software. No company on the planet is infallible, nor is any company unhackable. It is an expected and normal process for vulnerabilities to be discovered and remediated at each stage of software development. From the point of a developer writing code all the way to that finished product running in production.
You should expect any vendor you purchase hardware and software from to do the following, as Flock does:
- Threat modeling during the design phase of a product. (Structured thinking and questions around “what if” scenarios)
- Scanning and fixing code as the developer is writing it. (Static Code Analysis and Software Composition Analysis)
- Scanning and fixing finished code when a developer submits it to the code repository. (Static Code Analysis)
- Scanning and fixing applications running in production. (Dynamic Code Analysis)
- Continuously scanning and monitoring the infrastructure the application is running in. (Attack Surface Management and Vulnerability Scanning)
- Conducting penetration tests against all of the above. (Offensive security testing emulating real-world attacks)
There is a cliche about cybersecurity being an onion with many layers, and that remains accurate today. There is not one single thing a company does to reduce risk; it must be multi-stage and multi-phase to address the entire attack surface of a product.
How is Flock’s Cybersecurity team structured?
Flock continues to invest in our team and has 10 new headcount positions slated for hiring this year, adding to our existing team of 20+ engineers. Cybersecurity is nothing without people.
- Product Security & Privacy - This team is solely focused on our hardware and software products. Conducting architectural reviews, threat modeling, and the code scanning mentioned above.
- DevSecOps - Development and Security Operations, responsible for the cybersecurity of our cloud infrastructure, such as AWS.
- GRC Engineering - Governance, Risk and Compliance Engineering, ensuring we maintain our high level of cybersecurity standards across the business.
- Offensive Security & Vulnerability Operations - This team conducts penetration tests and offensive security research against our entire product line. They also manage all vulnerabilities across the business and product.
- Physical Security - This team ensures our physical security standards are maintained and that we can respond to threats against our physical office spaces.
- Incident Response & Adversary Pursuit - This team is responsible for responding to all suspected and real incidents, as well as continuously hunting in our environment for any and all possible intrusions.
All of our customers can review even more details about our cybersecurity program by visiting our Trust Center.
Readdressing Misleading Claims Made in a November 2025 YouTube Video
In November 2025, a YouTuber released a YouTube video with two other individuals claiming to have “hacked 80,000 Flock cameras”. That statement tells you all you need to know about the credibility of the individuals and the video itself. That claim is totally false and misleading. Had they actually hacked Flock, this would have been a federal crime under the Computer Fraud and Abuse Act of 1986, 18 U.S.C. § 1030.
What really happened was that in March 2025, an individual reached out to Flock via email, not through our bug bounty program. This bug bounty program is part of our responsible vulnerability disclosure process, which allows independent researchers to ethically research and submit vulnerabilities to Flock for cash compensation. These are very common programs that thousands of companies across the country maintain.
This individual illicitly acquired a Flock LPR camera, which was the focus of their research. Although this fell outside the scope of our bug bounty program, Flock offered to engage in good faith to review their findings, regardless of how the device was acquired illegally. The individual declined to participate in the ethical bug bounty program. Despite this, Flock reiterated its willingness to work in good faith to evaluate the findings.
Flock’s Product Security and Offensive Security teams evaluated the information submitted by this individual and determined that all of the findings were previously discovered by Flock’s cybersecurity team and were already fixed or planned for engineering sprints throughout the remainder of 2025. While the findings were legitimate, they were all of low severity. Meaning the risk to customers or customer data was near zero.
Further research by Flock’s Product Security and Offensive Security teams determined that the device this individual had illicitly acquired had also not been properly configured. It was never deployed to a customer and never received any standard software or security updates that happen automatically when a device is registered with our cloud. Had this individual not prevented it from connecting to our cloud, most of their findings would have been moot. As the device would have applied pending updates that would have fixed known issues.
Then, in November 2025, a YouTube video was released rehashing all the same findings that Flock had worked in good faith with this individual to address. No new vulnerabilities were revealed in this video.

Addressing Misleading Claims Made in a January 2026 YouTube Video on Flock PTZ Cameras
In January 2026, another video by the same YouTuber was released regarding Flock PTZ Cameras. As mentioned before, Flock has maintained an ethical vulnerability disclosure program and bug bounty program for many years. This individual did not ethically submit any information to Flock prior to the release of their video. Instead, the YouTuber made this discovery, chose to conceal it, traveled to a location of one of the cameras, filmed themselves reading a statement, then spent time editing their video for YouTube.
Flock devices use private IoT cellular networks to connect to the cloud. In 2025, one of our cellular carrier partners moved a small number of these Flock PTZ cameras from this private IoT network to the public cellular network used by cell phones. This exposed the camera's diagnostic interface to the internet for a short amount of time. This allowed for those cameras to be discovered on open-source services that constantly scan the internet and catalog the information in a searchable website. If you knew what to search for, you could then identify those few cameras on the internet.
This did not allow for any access to our cloud environment whatsoever. The diagnostic interface is just that: a feature used by our field technicians or privileged engineers to set up and troubleshoot these devices. There is no way to control the camera, or modify recorded video. I want to be clear, these cameras are installed in public spaces. You’d see nothing more than what you’d see standing directly under the camera in that public space.
Flock worked with our carrier partner to quickly resolve the network configuration issue. Flock has also built internal detections to detect such a rare change in the future. Flock has also modified the diagnostic interface to require our technicians to log in with a username and password. Again, this interface is intended to be usable when a technician is physically present. Regardless of how rare this network configuration error is, Flock has put in these compensating controls.

How does Flock secure its custom Android operating system?
Flock hardware runs on a heavily modified version of the Android operating system maintained by Google. This is an open-source operating system, meaning anyone in the world can look at the code and use it. Flock currently partners with Qualcomm, a world-leading semiconductor manufacturer, to supply various components for our devices, including the CPU. This is very different from the CPU in a computer running Windows or MacOS. Qualcomm’s chipsets are purpose-built and support specific operating system versions.
Qualcomm produces a custom, heavily modified version of Google Android that is designed to run on their chipsets. This can vary greatly from different versions of chipsets as well. From there, Flock modifies the Qualcomm version of Android even further for our specific device use cases, stripping out much of the functionality of the Android operating system used on mobile devices. A great example is SMS text messages; this capability is entirely nonexistent as it is unnecessary and unneeded code in an LPR camera.
Flock has never used Android Things, in any product.
Flock will continue to use and support our custom version of the Qualcomm Android operating system. We will continue to backport any necessary security patches, as required under our agreements with all customers. Those software updates will always be free of charge and happen automatically through Over-The-Air updates (OTA).
*Backporting is the process by which a vendor stops producing updates for a piece of software, and companies still using that software write their own patches.
Does Flock have qualified third-party attestations of its cybersecurity?
Yes, Flock has qualified third-party attestations of its cybersecurity. What you should also expect from your vendors is continuous audits by qualified, third-party firms. Flock takes this seriously and goes far beyond surface-level audits.
All of our audits are accessible to all of our customers on our Trust Center.
Flock maintains the following standards:
- SOC2 Type II, this is an opinion-based audit, not a certification. This is the bare minimum.
- Flock maintains several certifications:
- ISO 27001, Data Security
- ISO 27701, Data Privacy
- ISO 27017, Cloud Security
- ISO 27018, Privacy
- ISO 42001, AI
- Flock maintains standards for our Law Enforcement customers:
- CJIS Insights
- CJIS ACE
- FedRAMP 20x
- NDAA Compliant
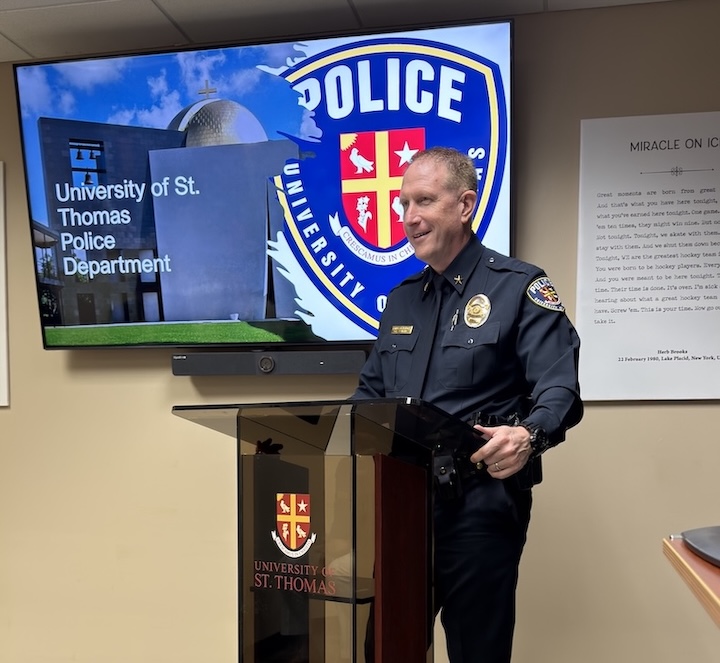
Flock also partners with our numerous customers to support their own independent security assessments of our products. Most recently, the Miami-Dade Sheriff's Office (MDSO) Cyber Crimes Bureau conducted an assessment of Flock LPR and found no issues. You can see our interview with Major George Perera here:
If you are an existing customer and interested in conducting your own authorized security assessment of our products, please reach out to your customer service representative.
Conclusion: Flock will continue to lead the industry in cybersecurity.
Cybersecurity is never done. It is a constant practice. I can’t promise that new vulnerabilities won’t be discovered, and I can’t promise that we can’t be breached; no company or CISO can promise that. If they do, run for the hills.
What I can promise is that Flock will continue to invest in the cybersecurity of our products and company and put our customers and their data above all else. I can promise we will continue to attempt to drive the risk of threats as close to zero as possible and be ready to respond in the event of a security issue.





Protect What Matters Most.
Discover how communities across the country are using Flock to reduce crime and build safer neighborhoods.

.webp)