Controlled Access for Everyone
Only approved users can access the system. Every search is recorded. Access is tied to a specific user account.
In plain terms: Access is limited and visible.
Data sharing is optional. If an agency chooses to share, this is done through conscious decisions, with clear rules outlining who can access what and the reasons for that access.
That means: Control stays with your local agency.
Who Can Access Flock Data?
Only users in approved roles can get access. They must use the system for a defined investigative reason within their agency.
ALPR Is Used for Public Safety Purposes
Authorized personnel within the agency
Users assigned approved roles
Case-related searches
Logged and reviewable access
ALPR Is Not Used for Casual Searching
General public access
Unauthorized officers
Open database browsing
In plain terms: No open access and no casual searching.
Access Is Restricted, Logged & Reviewed
Policy Defined Locally
Your local agency sets its own written rules for who can access the system and how it can be used.
Individual Authentication
Each user logs in with their own credentials. All activity connects to that specific person.
That means: No shared logins.
Purpose-Based Search
Searches must relate to a specific investigation and follow agency rules and the law.
Automatic Logging
Every search is recorded automatically. Supervisors can review activity.
In plain terms: Every search leaves a record.
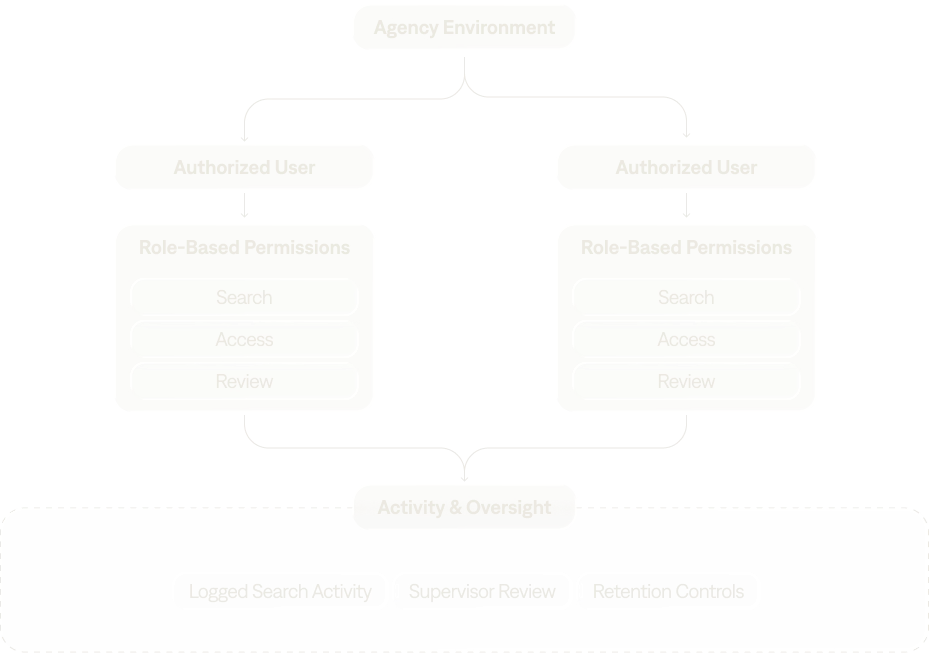
Each Agency Controls Its Own Access
Each agency controls its own settings and decides if, and when, to share data. Sharing never happens automatically.
If an agency chooses to share, participating agencies may see the shared data. That sharing is documented and controlled.
That means: Nothing is shared unless the agency turns it on.
How Misuse Is Mitigated
Purpose Limitation
Searches must include a reason tied to an investigation.
In plain terms: You cannot search without a purpose.
Query Logging
Every search is recorded and linked to the person who performed it.
Usage Review
Supervisors can review search activity to confirm it follows agency policy.
How Searches Are Audited & Reviewed
Every Search Logged
Each ALPR query is recorded with a user ID and time stamp. This documentation allows supervisors to see and review all searches.
Logs Available For Review
Supervisors and authorized staff can review search history.
Internal Agency Oversight
Supervisors can examine documentation and user behavior.
Transparency Mechanisms
Agencies can share policies publicly and explain how safeguards work.
In plain terms: Use is visible inside the agency.
How Network Sharing Is Controlled
Sharing is optional and documented.
Sharing Is Optional
Agencies choose whether to participate in network sharing.
That means: Participation is never automatic.
Agreements & Terms
Sharing follows legal requirements. Each agency defines who can access shared data and under what conditions.
Agency Policies
Agencies use their written policies and training reinforce responsible use.
Policy Violations
If someone misuses the system, the agency applies disciplinary action.
That means: Access depends on following the rules.
Frequently Asked Questions
Only authorized staff in approved roles within each agency can access the system. The public cannot search it. Officers without permission cannot use it. Every search is tied to a user account and recorded for supervisor review.
In plain terms: Access is limited and recorded.
No. Searches must relate to a specific investigation and follow agency rules and the law. Each search is recorded with a user ID and time stamp so supervisors can identify improper use.
That means: No unrestricted searching.
Use can be checked through recorded searches tied to individual users, plus supervisor review and agency policy enforcement.
In plain terms: There are policies in place to prevent misuse.
Data is never shared automatically. Sharing only happens if the agency gives clear permission. When sharing occurs, agencies can enforce their local rules & policies, including written agreements that define what can be shared and how it can be used.
That means: The agency that owns the data decides.
If a violation is found, the agency enforces its own disciplinary rules.
In plain terms: Misuse leads to consequences.

.webp)